
Threat intelligence and risk management headlined the RiskSec NY 2017 conference on May 2nd. This was a new event that evolved out of the SC Congress and was well produced and attended. What sets RiskSec apart from much larger events is the manageable bites of high-value content presented in personalized sessions. This offers cybersecurity professionals a means to take limited time out (on a more regular basis) to keep up with the dynamic and ever-evolving cybersecurity industry.
1. Obscurity doesn’t mean security
The opening keynote by Donald Freese (FBI) conveyed the importance of understanding why your enterprise may become a target for hackers. Haven’t we all heard of cases where obscurity did not necessarily mean secure? I regularly hear comments such as “who would want my data” and “our recipes aren’t secret.” It’s not necessarily about the value of your data — it’s the attack surface area that is the real threat. Take the Target breach for example — hackers moved laterally from a third-party vendor to Target’s POS system.
2. See the whole picture with behavioral analytics
While it may be some time before we consider removing the human analytical component of threat intelligence, machine learning enables us to trigger alarms and initiate defensive actions by identifying changes in baseline behavioral patterns.
“Lateral movement is the sweetspot to catch [hackers].” — Joe Mastromarino, Logrythym
3. Sharing vulnerability and breach data
There were several high-level discussions about tactical methods to collaborate and share vulnerability and breach information while eliminating the fear of repercussions (legal and otherwise) in doing so. Could a system like the FAA’s voluntary and confidential ASRS (Aviation Safety Reporting System) be a consideration?
4. Defense in Depth is NOT dead
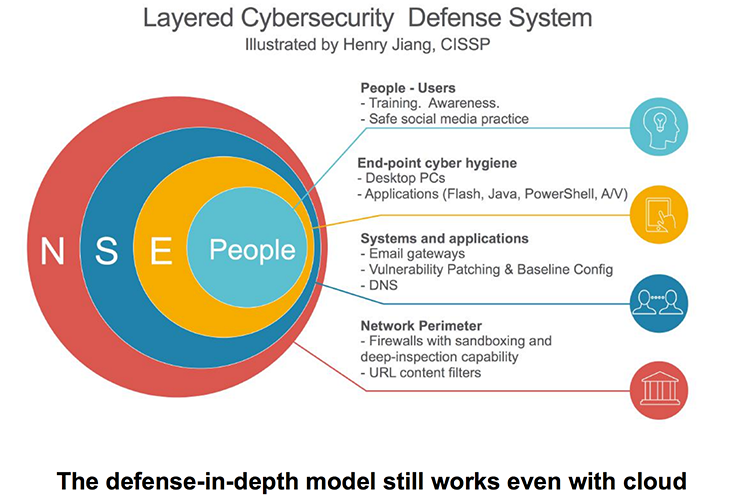
In fact, it is more relevant than ever.
5. Automating Incident Response
Before venturing into the world automation, it’s absolutely essential to understand your network infrastructure. Risk is always of interest to executives so key business drivers must be identified, understood, and aligned with your threat intel strategy. While financial services currently lead the pack in incident response automation, we’ll see more companies use machine learning to automate threat intelligence.
Great work by the SC Media team, conference organizers, sponsors, and speakers of RiskSec NY 2017! If you’re a cybersecurity professional, I highly recommend attending future RiskSec events. It’s an excellent opportunity to continue honing your skills and stay abreast of the latest developments in the cybersecurity landscape.
For more insight into managing threat intelligence and risk, check out these resources:
Click here to subscribe to the blog
Follow @Idenhaus and connect with Hanno on LinkedIn.
By going to work quickly to solve the most challenging cybersecurity and identity management problems, Idenhaus takes the pain out of securing corporate information and assets for companies that aspire to maximize their potential in this digital age. Click here to contact us






