A Key Identity Management Data Point: Workarounds

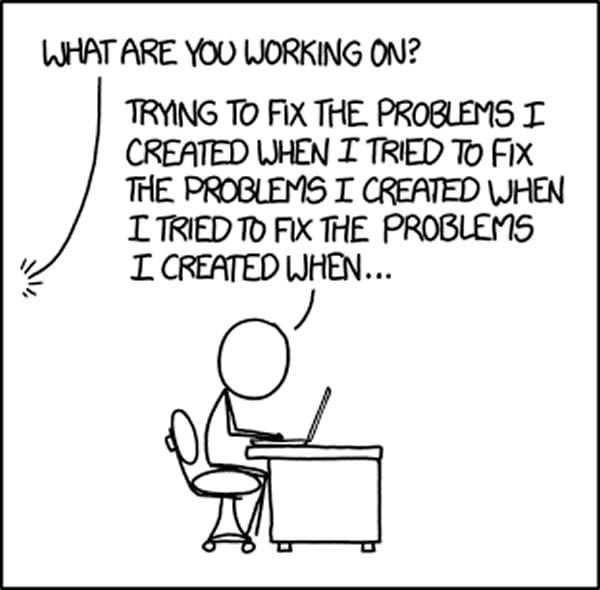
A workaround is defined as a temporary fix that normally implies that a genuine solution to the problem is needed. Workarounds are bad, it means that people are having to do things outside your solution in order to be effective. That is, there is a limitation in your process or system that requires folks to ‘get creative’ to mitigate that issue. When it comes to Identity & Access Management, the fewer workarounds your organization has, the more mature your IAM program.
Here is why workarounds are a key indicator of the maturity of your IAM solution.
When IAM systems are implemented they touch a broad range of users and systems. Initially, the biggest impact is the change to the way workers are onboarded into applications and systems. This change directly impacts the onboarding processes that HR, line managers, and IT use on a daily basis. The effectiveness of your IAM solution rests in whether these departments willingly adopt the new systems. Oftentimes, organizations face challenges with these new processes, and workarounds are artfully developed by the users. Workarounds allow users to live with the new processes and system while avoiding some of the demands of the IAM system that they perceive to be unreliable or ineffective. For example, in urgent situations, administrators could enter new user records in the IAM system before receiving a feed from the HR system. Alternatively, the user account might have been requested via email or a support ticket by the manager and would be fulfilled by an IT Admin.
These workarounds undermine worker productivity, impact the end user experience, and often indicate a misalignment between HR processes and IT. As such, workarounds are a key indicator of the maturity of your IAM solution; the fewer workarounds you have, the more mature your solution. Processes are not always the easiest to work on and it takes effort and time to properly develop processes that function and make sense in your operational environment. However, the expense is worth the investment.
Click here to subscribe to the blog
Follow @Idenhaus and connect with Hanno on LinkedIn.
Photo credit: Flickr
By going to work quickly to solve the most challenging cybersecurity and identity management problems, Idenhaus takes the pain out of securing corporate information and assets for companies that aspire to maximize their potential in this digital age. Click here to contact us today!







2 thoughts on “Why Workarounds Are IAM’s Silent Killer”
Workarounds give you a false sense of security.
Agreed! Workarounds make it appear from the outside that the system is working, when it is actually falling short. These alternate paths can only compensate for so long and are ultimately not scalable. So the organization is not able to handle rapid growth or absorb large changes such as a reorganization. To your point, things appear to be better than they are!